Recent Posts
- Integrating AI with conventional software
- From Ethical Duty to Legal Imperative: The Crucial Role of Secure Development in Today’s Software Industry
- Gone Phishing: Personalizing mass phishing with AI
- Elements of a secure development life-cycle
- Six Successful Strategies For Re-Opening Your Business After Covid19
- Cybersecurity Readiness in a Pandemic Era
- Cybersecurity In 2020 – A Roadmap To Keeping Your Business Safe
- What’s your reputation worth? The cost of not protecting your data.
- Ryuk Ransomware Hits Canadian Businesses
- Why Are Small Businesses A Hackers Playground?
- Phishing attacks targeting Office 365 users
- The new normal in cybersecurity
- Hackers targeting torrent sites
- The implications of PIPEDA for small business
- Cybersecurity Essentials
Phishing attacks targeting Office 365 users
By Dominic Chorafakis, P.Eng, CISSP – March 20, 2019
Email continues to be the favorite tool for hackers to hijack computers and steal information. Recent phishing campaigns are proving to be particularly effective by combining different techniques to target Office 365 users. There are two key elements that make the attack effective:
- Malicious messages appear to arrive from known contacts
- Messages contain PDF attachments which do not carry any malware so they get past anti-virus. The goal is to entice users to click on a link that appears to take them to OneDrive or Office 365
Taking the time to verify the email address that a message appears to be from is an important step in security awareness. Some times the domain portion of the email address (the part that comes after the @ sign) will be a clue that the sender isn’t really who they claim to be. Unfortunately, it is not enough to just look at the From field, the sender’s email account may have been hacked, but also sophisticated hackers are able to spoof the From field to make it look like an email was sent by someone else.
It is important to note that this is not personal or specifically targeted, so don’t assume you are safe just because hackers don’t know who you are. Once a computer becomes infected, the malware will automatically extract information from contact lists and earlier email messages and automatically launch a similar attack against those contacts. It doesn’t even need to be someone you know who was infected. Say your friend Bob sends you an email inviting you to a party, and copies you and 10 other people you don’t know. If any one of those 10 people are infected, the malware will try to send an email from Bob to your email address with the malicious PDF without ever knowing you or Bob personally.
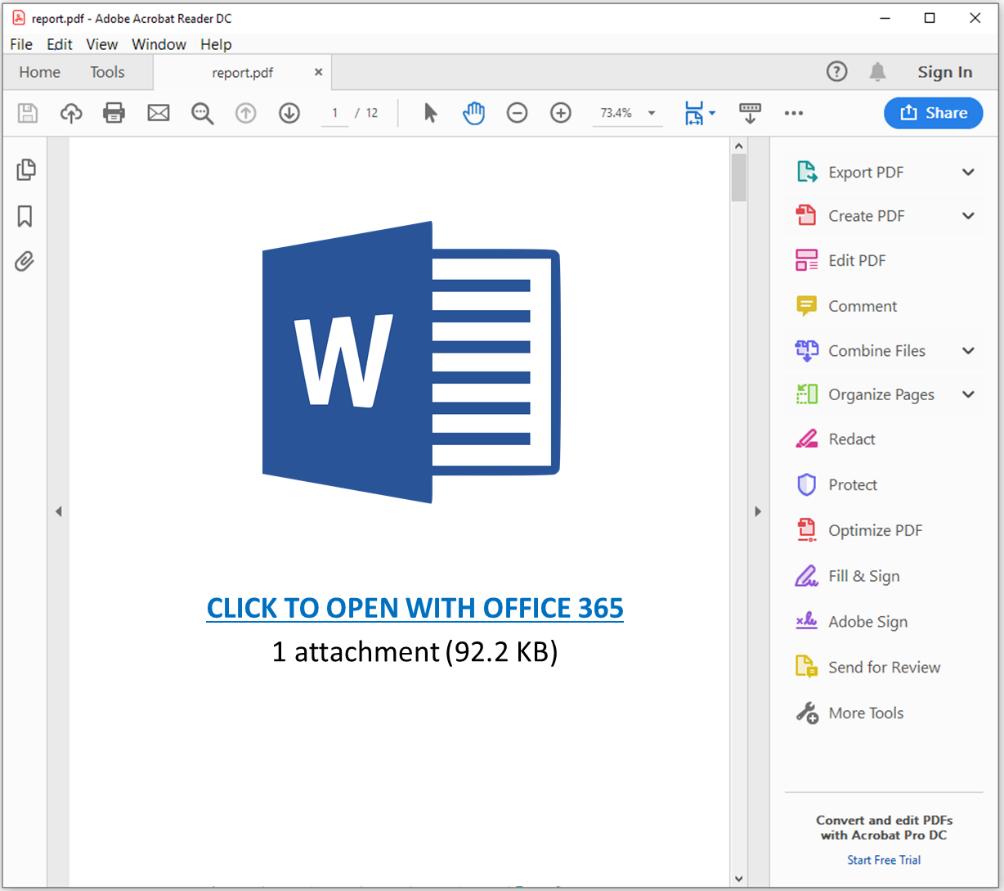
The malicious email may contain a link in the message itself, but in this case, we are focusing on the attack specifically targeting Office 365 users. In those attacks, when you open the PDF file, it will try to get to click on what looks like a legitimate link, here’s an example
If a user is tricked into clicking on the link, what happens next depends on the specific type of attack.
In some cases, the user is directed to a website that looks like a real Office 365 login page as seen below.
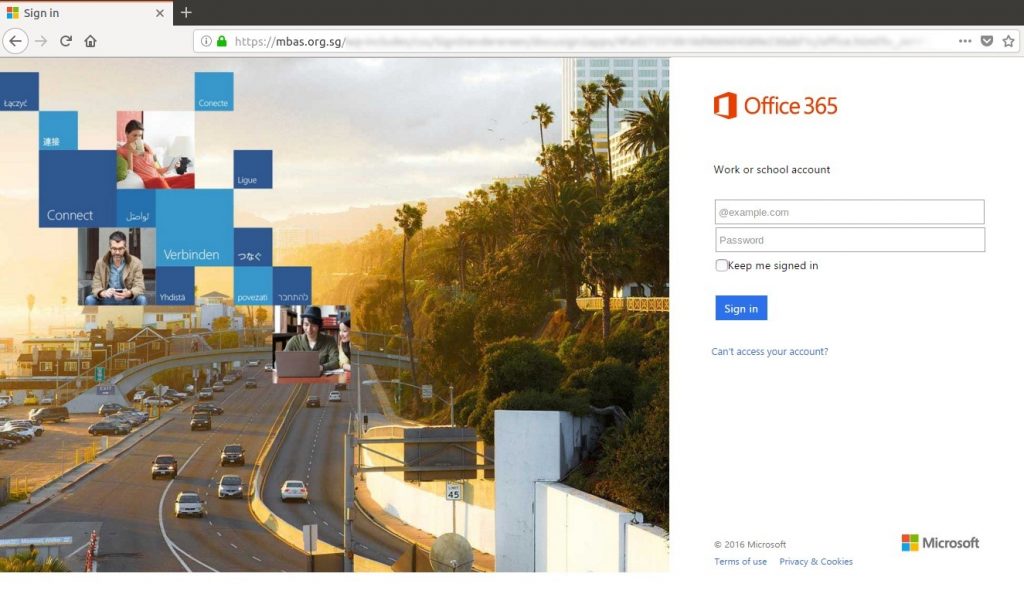
Note the URL in the browser is not Microsoft’s at all.
In this case the attacker is trying to trick the user into providing their username and password which will be sent to the hacker instead of Microsoft.
In other cases, clicking on the link will take to you a website that hosts software known as an Exploit Kit that will attack your PC looking for a vulnerability that can be used to install malware on it.
What to do
- Be suspicious of any email with a PDF attachment even if it appears to come from someone you know. If it is unusual (e.g. someone sends you an invoice or other document you are not expecting), do not open the attachment.
- If you suspect an email may be a scam, do not reply to that email to verify its authenticity if you have other means of contacting them.
- If you do open the attachment and see a Word or Excel logo prompting you to click on a link to open the document in Office 365
- Do not click on that link
- Notify your IT administrator immediately
- Close the attachment immediately
- Run a full virus scan on your system
- If you do click on the link before you realize it is a scam
- Power down your computer
- Notify your IT administrator immediately
The new normal in cybersecurity
By Dominic Chorafakis, P.Eng, CISSP, January 19, 2019
Not so long ago, computer viruses were mostly created by pranksters and computer geeks trying to see what they could get away with. There was still some risk for data loss and downtime, but for the most part viruses were just an annoyance and installing a decent anti-virus was enough to keep your systems safe.

Today things are much different. Online banking and bitcoin have made it possible and safe for hackers to turn what used to be a misguided hobby into an organized criminal enterprise, with cybercrime proceeds surpassing $ 1 Billion last year.
The lone computer geek has been replaced with sophisticated teams of highly skilled professional hackers creating military grade malware that is able to bypass anti-virus and selling access to it on the “dark web”, a kind of Internet parallel universe that is only accessible through special software which allows its users to remain anonymous and untraceable.
This new reality means that a business-as-usual approach to cybersecurity is no longer enough. Unfortunately, many small and medium business owners believe that cyber criminals won’t target them because they are too small or have nothing that hackers would want and don’t take the necessary steps until it’s too late.
Fortunately, there are some simple and cost-effective steps that businesses can take to reduce risks and avoid potentially significant repair costs and losses due to unplanned downtime.
Apply software updates and patches
Users should check for and apply software updates provided by vendors and this activity should be prioritized:
- Firewalls and Routers exposed to the internet
- Externally accessible servers
- Internal servers and personal computers
- Other infrastructure such as security cameras or other internet-enabled devices
Reduce network footprint
Businesses often create firewall rules to allow employees, vendors or other third parties to access IT systems remotely. Firewall misconfigurations, or intentional creation of rules that are too broad in scope and allow access from anywhere on the internet is a common cause of security breaches.
Firewall rules should be reviewed and the number of systems that are exposed to the internet should be kept to a strict minimum. When network ports are forwarded to allow external access to IT systems, the rules should be restrictive and limit access only from a specific set or range of external IP addresses.
When possible, vulnerability scans should be performed to confirm that firewall rules are correctly restricting access to IT systems.
Perform secure backups
Up-to-date backups are critical in order to quickly recover from an attack with minimal impact to business systems. Backup policies should take into consideration that infected systems with access to mounted backup drives may also encrypt backup files. This risk should be mitigated by having a backup strategy that keeps historical versions of backed up files and includes snapshots that are not accessible to systems that may become infected.
Deploy professional anti-virus
While zero-day attacks are an unfortunate reality, the fact is that the vast majority of breaches are caused by known vulnerabilities that professional anti-virus solutions know about and are able to block. Commercial anti-virus software should be installed and licensed on all systems and configured to automatically update virus definitions from the vendor. Additional security features provided by many commercial solutions like secure browsing extensions, identity theft protection and enhanced computer firewall features should be enabled on all computers.
Cyber Security Awareness
Studies show that the chance of a breach is reduced by up to 40% in businesses that engage in cyber security awareness training.
The method most commonly used by hackers to bypass security measures is phishing, where users are tricked into clicking on a link or opening an attachment in an email that looks like it came from a legitimate source like a customer, vendor, bank or other well-known company or website.
Computer users should take time to educate themselves on spam and phishing techniques as well as tips on how to detect them and ways to avoid falling victim. There are many free resources online such as staysafeonline.org that provide information and tips for businesses and individuals.
Managed Security Services
Cyber-security is constantly evolving as the cat-and-mouse game between cyber criminals and security vendors rages. Installing a firewall and anti-virus and then simply forgetting about cyber-security can be a huge and costly mistake. Businesses should consider managed cyber-security services to make sure IT systems and staff are protected against the most current threats and vulnerabilities.
Hackers targeting torrent sites
By Dominic Chorafakis, P.Eng, CISSP – December 5, 2019
There has been a surge of hacks targeting torrent users by posting fake ads on popular peer-to-peer file sharing sites that direct victims to websites infected with exploit kits able to install information-stealing malware and ransomware on their computers.

Torrents are a common source of malware and viruses since the very nature of peer to peer file sharing means that the files you are downloading can come from anyone and anywhere. As a general rule you should not install torrent clients, and only download files from known, reputable sources.
If you insist on using torrents, you should assume that the computer you are using will be hacked and don’t use it for activities like banking or accessing your email. If possible keep it on a separate network by setting up a guest WiFi network that doesn’t have access to the rest of your network.
What you should do
Take the following measures to protect your systems from this attack:
- Inform your staff that hackers are targeting Torrent users and that accessing file sharing sites is prohibited
- Prohibit the use of peer-to-peer file sharing clients like uTorrent on computers connected to your network
- Ensure that all computers have the latest operating system and browser patches installed
- Consider using a reputable ad-blocker
To receive important cybersecurity updates on the latest threats with tips on how to stay safe click on this button to follow us on LinkedIn or join our critical updates mailing list at My Security Console.
The implications of PIPEDA for small business
By Dom Chorafakis, P.Eng, CISSP, November 27, 2018
DISCLAIMER
Information contained in this post is intended as general information only. It is not, nor should be construed as legal advice and should not be relied upon as such. If you need legal advice, please contact an attorney directly.
Personal Information Protection and Electronic Documents Act (PIPEDA)
It has been almost a month since the new PIPEDA rules regarding mandatory breach reporting in Canada came into effect and many clients still have questions around what it means for their business. In this post we’ll explore some of the key highlights of the legislation and provide links back to the relevant sections of the Office of the Privacy Commissioner of Canada (OPC) website you can use to get more information.

Perhaps the most common question that comes up is whether the rules apply to a small business that only has one or two employees. The short answer is yes, they do. The rules do not provide for any exemptions based on number of employees or revenue. There are however certain types of organizations to which the rules may not apply as per the PIPEDA brief available at https://www.priv.gc.ca/en/privacy-topics/privacy-laws-in-canada/the-personal-information-protection-and-electronic-documents-act-pipeda/pipeda_brief/ [1]:
“Unless they are engaging in commercial activities that are not central to their mandate and involve personal information, PIPEDA does not generally apply to:
- not-for-profit and charity groups
- political parties and associations” [1]
So if you own a business that is not a charity, political party or association, then the rules definitely apply to you. Note however that even those organizations may need to comply with the rules if “they are engaging in commercial activities that are not central to their mandate” [1]. For example, if an association sells its member list data for marketing purposes, PIPEDA would apply.
As mentioned in the brief, “PIPEDA applies to the collection, use or disclosure of personal information in the course of a commercial activity. A commercial activity is defined as any particular transaction, act, or conduct, or any regular course of conduct that is of a commercial character, including the selling, bartering or leasing of donor, membership or other fund-raising lists.” [1]
The personal information that is protected under PIPEDA includes anything that is recorded about an identifiable individual. According the brief, “This includes information in any form, such as:
- age, name, ID numbers, income, ethnic origin, or blood type;
- opinions, evaluations, comments, social status, or disciplinary actions; and
- employee files, credit records, loan records, medical records, existence of a dispute between a consumer and a merchant, intentions (for example, to acquire goods or services, or change jobs).” [1]
The Act defines 10 fair information principles that businesses must follow with regards to personal information:
- Accountability
- Identifying Purposes
- Consent
- Limiting Collection
- Limiting Use, Disclosure, and Retention
- Accuracy
- Safeguards
- Openness
- Individual Access
- Challenging Compliance
There are a number of clauses in the Act (which is available online at http://laws-lois.justice.gc.ca/eng/acts/P-8.6/FullText.html [2]) that are relevant from a cybersecurity perspective. For example, the Act states that “Organizations shall implement policies and practices to give effect to the principles, including
(a) implementing procedures to protect personal information;
(b) establishing procedures to receive and respond to complaints and inquiries;
(c) training staff and communicating to staff information about the organization’s policies and practices; and
(d) developing information to explain the organization’s policies and procedures.” [2]
Furthermore, the Act states that “The methods of protection should include
(a) physical measures, for example, locked filing cabinets and restricted access to offices;
(b) organizational measures, for example, security clearances and limiting access on a “need-to-know” basis; and
(c) technological measures, for example, the use of passwords and encryption.”
Not only does the act require businesses to use appropriate administrative and technological safeguards to protect personal information, it also stipulates that any breaches of these safeguards that expose this personal information must be reported to the OPC. Organizations who fail to report such a breach may be liable for a fine of up to $100,000. According to the Act, “An organization shall report to the Commissioner any breach of security safeguards involving personal information under its control if it is reasonable in the circumstances to believe that the breach creates a real risk of significant harm to an individual.
[…] significant harm includes bodily harm, humiliation, damage to reputation or relationships, loss of employment, business or professional opportunities, financial loss, identity theft, negative effects on the credit record and damage to or loss of property.” [2].
The OPC provides a privacy toolkit for business at https://www.priv.gc.ca/en/privacy-topics/privacy-laws-in-canada/the-personal-information-protection-and-electronic-documents-act-pipeda/pipeda-compliance-help/guide_org/ to help comply with the Act and its principles.
Cybersecurity Essentials
By Dom Chorafakis, P.Eng, CISSP, June 21, 2017
The cyber threat landscape is constantly changing as criminal hackers look for new and creative ways to profit from online crime. While there is no silver bullet that can guarantee protection against breaches or other forms of attack, keeping up to date with the latest threats and vulnerabilities is an important part of any security strategy.
Cryptojacking
With the rise in popularity of digital currencies like Bitccoin and Etherium, cybercriminals have found new opportunities in cryptomining as a revenue stream. The unauthorised use of computer resources to mine cryptocurrency known as cryptojacking has now exceeded ransomware as the largest online threat. There are two aspects to this that are important to take into account from a security perspective: website compromises and malvertising.
 Hackers attempt to install cryptomining software on victims’ computers by installing malicious code on websites they are able to compromise. Web servers have always been vulnerable to hackers because of their very nature, but the potential for profit from illicit cryptomining makes them more interesting targets than ever before. System administrators need to ensure that servers are adequately protected by making sure the operating system and software is up to date, accounts are secure and use strong passwords, endpoint security mechanisms like anti-virus is installed, servers are protected using Intrusion Prevention technology, and that measures are in place to detect and prevent unauthorised content changes.
Hackers attempt to install cryptomining software on victims’ computers by installing malicious code on websites they are able to compromise. Web servers have always been vulnerable to hackers because of their very nature, but the potential for profit from illicit cryptomining makes them more interesting targets than ever before. System administrators need to ensure that servers are adequately protected by making sure the operating system and software is up to date, accounts are secure and use strong passwords, endpoint security mechanisms like anti-virus is installed, servers are protected using Intrusion Prevention technology, and that measures are in place to detect and prevent unauthorised content changes.
Malvertising
In addition to compromising legitimate websites, hackers are creating fraudulent sites that look legitimate, directing users to these sites using fake online ads displayed on popular websites, a practice known as malvertising. This practice is not new, but a significant spike in cryptojacking related malvertising was recently observed by a network of Intrusion Prevention systems as reported here.
People surfing the internet should assume that at some point they will come across either a legitimate site that has been compromised, or a fraudulent site set up specifically to infect vulnerable systems. To protect themselves, users should keep their Operating System and all software they use up to date, make sure good anti-virus is installed and up to date, use safe-browsing plugins from their anti-virus vendor and use an ad-blocker to block online ads.
Email compromise
While there has been a significant increase in these new threats thanks to the potential for quick profit, email continues to be by far the predominant attack vector. From account compromise and phishing attacks to malicious attachments, email based attacks are still the most common method used by hackers to infect vulnerable systems with ransomware, cryptojacking software, or trojans used to carry out financial fraud and other attacks. While technologies like anti-spam and anti-virus can help, user education is one of the most effective tools to help minimise risk in this area. Users need to be aware of the types of threats and attacks, how to identify them, and what steps they must take in the event of a suspected compromise.
The long game
Staying up to date with the latest threats and cyberattacks is important, but is only one element of a good cyber security strategy. Defending against hackers and cyber criminals is not a onetime activity, it needs to be an ongoing process that is actively managed and updated to reflect the changes to your information, its ecosystem and evolving threats. A good strategy includes the following five elements.
1. Identify your assets
It’s impossible to build a solid defence if you don’t know exactly what you are defending. During this stage you need to identify all of the data, applications and hardware that need to be protected.
2. Identify threats and risks
Once you have a list of everything that needs to be protected, it’s time to analyse the risks and threats to each asset. The threats to your company website are different than the threats to your customer list or payroll information, so different countermeasures are needed to protect the confidentiality, integrity and availability of the systems and the information they process.
3. Apply security controls
Once you have identified and prioritized assets and threats, it is time to select and deploy the safeguards needed to protect your organization. This may seem daunting but remember that you don’t need to solve everything at once, you can start by taking steps to address the biggest risks to your most valuable or sensitive assets and work down the list as time and budget permits.
4. Detect and Respond
Despite best efforts breaches and other security incidents can and will occur. The ability to detect and respond to them is as important as the effort to prevent them in the first place. There are a number of steps that can be taken in this area ranging from technical solutions such as managed security services and Intrusion Prevention, to policies and procedures such as having a formal Incident Response Plan.
5. Review and adjust
Lastly, it is important to keep in mind that a cyber security strategy is not static, it needs to be reviewed and adjusted to make sure it is always up to date and your important assets are protected. How often it needs to be reviewed depends on many factors including the threat level, sensitivity of information, as well as legal and regulatory requirements. At a minimum the strategy should be reviewed at least once a year, every time there is a significant IT change and every time there is a security incident.
Where to go from here
There are many free resources that can help individuals and businesses with cyber security. In Canada the government has launched a Get Cyber Safe initiative with the mission “to educate Canadians about Internet security and the simple steps they can take to protect themselves online”. For more information you can visit the Get Cyber Safe website and get started on your own cyber safety strategy.
Ask an expert
If you have a question about one of our blog posts or cybersecurity in general, our experts are happy to help.
 Cisco Talos Blog
Cisco Talos Blog
- Getting a career in cybersecurity isn’t easy, but this can help
- Decrement by one to rule them all: AsIO3.sys driver exploitation
- Cybercriminal abuse of large language models
- A week with a "smart" car
- When legitimate tools go rogue
- Famous Chollima deploying Python version of GolangGhost RAT
- Know thyself, know thy environment
- catdoc zero-day, NVIDIA, High-Logic FontCreator and Parallel vulnerabilities
- Microsoft Patch Tuesday for June 2025 — Snort rules and prominent vulnerabilities
- Everyone's on the cyber target list
 CISO Online
CISO Online
- Three steps to boost Amazon S3 data security
- Scattered Spider nimmt Luftfahrtbranche ins Visier
- Siloking von Ransomware-Attacke betroffen
- Scattered Spider shifts focus to airlines with strikes on Hawaiian and WestJet
- Patch now: Citrix Bleed 2 vulnerability actively exploited in the wild
- Gefährliche Lücke in Brother-Druckern
- Microsoft hints at revoking access to the Windows kernel — eventually
- Cybercriminals take malicious AI to the next level
- Beyond CVE: The hunt for other sources of vulnerability intel
- Die besten XDR-Tools
 Krebs On Security
Krebs On Security
- Inside a Dark Adtech Empire Fed by Fake CAPTCHAs
- Patch Tuesday, June 2025 Edition
- Proxy Services Feast on Ukraine’s IP Address Exodus
- U.S. Sanctions Cloud Provider ‘Funnull’ as Top Source of ‘Pig Butchering’ Scams
- Pakistan Arrests 21 in ‘Heartsender’ Malware Service
- Oops: DanaBot Malware Devs Infected Their Own PCs
- KrebsOnSecurity Hit With Near-Record 6.3 Tbps DDoS
- Breachforums Boss to Pay $700k in Healthcare Breach
- Patch Tuesday, May 2025 Edition
- Pakistani Firm Shipped Fentanyl Analogs, Scams to US
 The Hacker News
The Hacker News
- U.S. Agencies Warn of Rising Iranian Cyberattacks on Defense, OT Networks, and Critical Infrastructure
- Europol Dismantles $540 Million Cryptocurrency Fraud Network, Arrests Five Suspects
- Blind Eagle Uses Proton66 Hosting for Phishing, RAT Deployment on Colombian Banks
- Leveraging Credentials As Unique Identifiers: A Pragmatic Approach To NHI Inventories
- ⚡ Weekly Recap: Airline Hacks, Citrix 0-Day, Outlook Malware, Banking Trojans and more
- FBI Warns of Scattered Spider's Expanding Attacks on Airlines Using Social Engineering
- GIFTEDCROOK Malware Evolves: From Browser Stealer to Intelligence-Gathering Tool
- Facebook’s New AI Tool Asks to Upload Your Photos for Story Ideas, Sparking Privacy Concerns
- Over 1,000 SOHO Devices Hacked in China-linked LapDogs Cyber Espionage Campaign
- PUBLOAD and Pubshell Malware Used in Mustang Panda's Tibet-Specific Attack